AI Startups: Navigating Extortion, Allegations & Leadership Crises
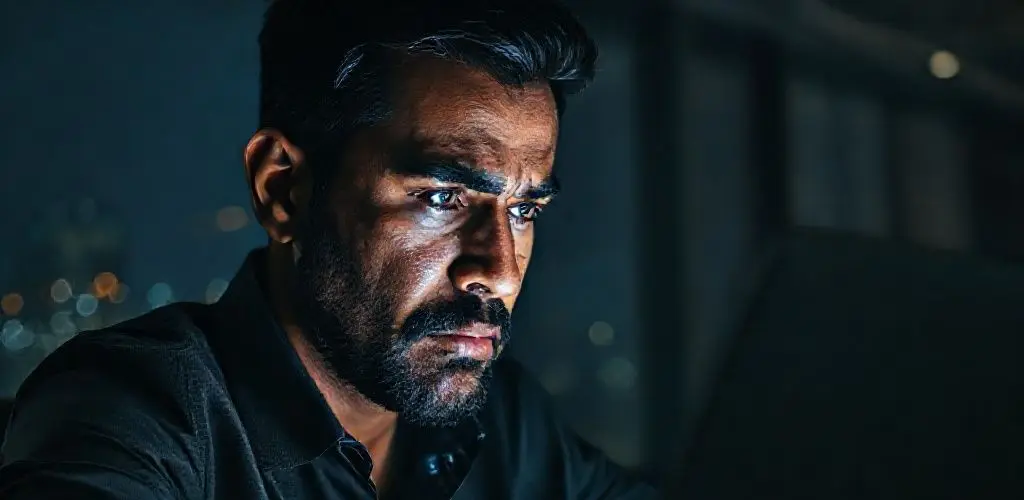
The late San Francisco fog clung to the windows, a familiar shroud on a December night.
Inside, the only light in the otherwise dark room came from a laptop screen, casting a stark glow on a tech CEO’s face.
He traced the lines of text again, a cold dread settling deep in his gut.
A demand.
Millions of dollars in cryptocurrency.
His AI startup, the company he poured his life into, was being blackmailed.
This was not just about money; it was about trust, about the reputation painstakingly built, now threatened by a shadowy group wielding illegally obtained confidential information.
The digital world, once a boundless frontier of opportunity, had become a battleground.
In that quiet moment, the weight of the entrepreneurial journey felt heavier than usual.
Beyond the audacious demand, there were whispers, too—allegations from former employees painting a picture starkly different from the startup’s public image.
This dual crisis, playing out in encrypted emails and the harsh glare of public social media, highlights the complex vulnerabilities inherent in today’s high-stakes, fast-paced tech landscape.
Even as the AI sector surges, it attracts both incredible success and insidious digital threats.
In short: A fast-growing AI startup faces a significant crypto extortion attempt involving stolen confidential data.
Simultaneously battling public allegations of unethical practices and a toxic work environment, this case highlights the complex challenges high-growth tech ventures encounter in the digital age.
Why This Matters Now: Navigating the AI Frontier’s Dark Side
The meteoric rise of AI startups often garners headlines for their disruptive potential and impressive funding rounds.
Yet, beneath the veneer of innovation and venture capital success lies an increasingly complex terrain of digital threats and reputational hazards.
This incident, where a fast-growing AI firm finds itself at the epicenter of both an external extortion scheme and internal dissent, serves as a poignant case study for the entire tech ecosystem.
It underscores that rapid growth, while exciting for a tech startup, can inadvertently create vulnerabilities.
This scenario compels leaders to look beyond product development and consider the robust infrastructure needed to withstand a multi-pronged assault on their company’s integrity.
Rapidly scaled operations, though essential for competitive advantage, can become potent magnets for malicious actors if not fortified with comprehensive cybersecurity and strong ethical governance.
It is a sobering reminder that success demands unyielding vigilance in every dimension of a modern business.
The Anatomy of a Digital Siege: A Startup’s Crisis Unpacked
At its core, this particular company’s challenge involved a two-front war: a digital extortion plot layered with serious public accusations about its internal conduct.
The CEO of this prominent AI startup publicly revealed that his company was being targeted.
A small group, having illegally obtained confidential information, demanded a substantial sum in cryptocurrency.
The perpetrators threatened to release manipulated data and false allegations unless their demands were met.
This digital blackmail is not just about data theft; it is about weaponizing information and twisting narratives.
A counterintuitive insight here is that moments of significant achievement, like securing growth funding or launching a groundbreaking product, can actually increase a company’s risk profile, making it a more attractive target.
Success, it seems, casts a long, vulnerable shadow, necessitating heightened cybersecurity and crisis management protocols.
A Voice from Within: Employee Allegations Surface
Compounding the external threat were the public allegations from former employees.
A former staffer openly accused the company of various unethical practices, including claims of workplace mistreatment and a toxic work environment.
The former employee characterized the work culture as severely challenging, citing arduous working conditions and unfulfilled compensation promises.
Such claims, even when disputed, indicate potential employee dissatisfaction that can be exploited by external actors.
The CEO unequivocally denied all allegations, calling the claims wildly false and defamatory.
He contended that the data was being manipulated out of context to harm the startup, particularly after a period of significant growth.
This clash of narratives highlights the intense pressure on leadership to manage both external threats and internal grievances, demonstrating the critical need for a resilient organizational culture.
What This Case Reveals About Modern Tech Threats
- Confidential Data is a Weapon: The extortion attempt explicitly leveraged illegally obtained confidential information.
The implication is clear: any sensitive data, from client lists to internal communications, is a potential tool for blackmail.
The practical need is robust cybersecurity and data governance, which are no longer just IT concerns but core components of comprehensive risk management and brand reputation protection.
- Reputational Damage Can Be Orchestrated: The threat to release manipulated data and false allegations demonstrates how easily digital narratives can be twisted.
Public perception can be engineered for malicious purposes, causing immense damage to a company’s image.
Companies must prioritize proactive reputation management, establishing clear communication protocols and swiftly addressing misinformation to maintain trust.
- Growth Attracts Both Capital and Criminality: Significant funding rounds and periods of rapid expansion often signal increased visibility and perceived wealth, making companies more attractive targets for cybercriminals.
A practical implication is that post-growth due diligence must extend beyond financials to include comprehensive security and HR assessments, anticipating new vulnerabilities that come with scale.
- The Interplay of External Threats and Internal Dynamics: The coexistence of the extortion scheme and employee mistreatment allegations points to a complex interplay.
Vulnerabilities, whether real or perceived, can be exploited, turning internal discontent into fodder for external attacks.
Businesses must foster a transparent and ethical corporate culture, addressing employee concerns proactively to prevent internal issues from becoming external weaknesses.
A Playbook for Navigating Digital Blackmail & Reputation Threats
- Immediate Crisis Response & Law Enforcement Engagement: Immediately report any extortion attempt to law enforcement.
Engaging legal counsel specializing in cybersecurity and corporate crime is paramount, establishing a company’s intent to fight rather than succumb.
This demonstrates integrity and a commitment to protecting assets.
- Fortify Your Digital Perimeter: Conduct an urgent, comprehensive audit of all digital assets and network security.
Focus on identifying how confidential information could be breached and implementing immediate corrective measures, including enhanced encryption, multi-factor authentication, and employee training.
- Proactive and Transparent Communication Strategy: Control your narrative by issuing clear, factual statements addressing allegations.
Avoid speculative comments and focus on verifiable information.
For complex situations, prepare a detailed FAQ for stakeholders to proactively combat misinformation and manage public perception.
- Conduct a Deep Dive into Corporate Culture & Employee Feedback: Seriously investigate any employee allegations, even while refuting their public manipulation.
Foster open channels for feedback and address grievances promptly and respectfully.
An open culture reduces the likelihood of internal issues becoming public vulnerabilities.
- Pursue Legal Recourse Aggressively: Actively follow through on legal action against perpetrators of extortion and defamation.
This demonstrates commitment to integrity, can deter future attacks, and reinforces a zero-tolerance policy against illegal activities, protecting the company’s long-term interests.
- Build a Resilient Ethical Framework: Embed a strong ethical core into your company’s DNA.
This includes clear policies on data handling, employee conduct, and whistleblower protection, acting as a powerful safeguard against internal decay and external manipulation, fostering trust both internally and externally.
The Ethical Tightrope: Risks, Trade-offs, and Safeguards
Navigating a crisis of this nature involves significant risks and complex trade-offs for an AI startup.
The primary risk is irreparable damage to the company’s reputation and stakeholder trust.
Operational disruption, financial strain from legal battles, and potential investor flight are also major concerns, impacting long-term sustainability and growth.
A critical trade-off is between complying with extortion demands versus fighting them, a path many ethical companies choose by involving law enforcement.
Another involves transparency: how much information to release publicly without compromising ongoing investigations or legal action, requiring careful calibration of public statements.
Mitigation demands an unwavering commitment to ethical leadership.
Companies must implement robust internal reporting mechanisms, ensuring employees feel safe to raise concerns without fear of reprisal.
Regularly scheduled crisis simulations can prepare leadership teams for rapid, coordinated responses, enhancing overall crisis management capabilities.
An ethical framework that prioritizes people and principles over short-term gains acts as a powerful safeguard against these multifaceted threats.
Monitoring & Resilience: Tools, Metrics, and Cadence
Recommended Tool Stacks:
Enterprise-grade cybersecurity platforms, threat intelligence feeds, and data loss prevention (DLP) tools are crucial.
Additionally, social listening and reputation management tools are necessary for real-time tracking of brand mentions, sentiment analysis, and identifying emerging narratives across social media platforms.
Anonymous feedback platforms, regular employee pulse surveys, and human resources information systems help monitor internal employee sentiment.
Key Performance Indicators (KPIs) for Crisis Resilience:
Social Sentiment Score measures public perception of the company’s brand, with a target of neutral to positive.
Employee Net Promoter Score (eNPS) measures employee loyalty and satisfaction, with a target of consistently high scores.
The Security Incident Rate tracks the number of attempted or successful breaches, with a target of zero or minimal incidents.
Negative Media Mentions measure the volume of critical press or social posts, with a target to minimize them.
Review Cadence:
Daily monitoring of social media and security alert reviews are essential.
Weekly leadership check-ins on crisis status and internal communications updates ensure agile responses.
Quarterly employee culture audits and comprehensive cybersecurity posture reviews provide deeper assessments.
Annually, external risk assessments and crisis management plan revisions ensure the company remains prepared for evolving threats.
FAQ
How can AI startups protect against extortion attempts?
AI startups can protect against extortion by implementing strong cybersecurity measures, including data encryption and access controls, and by training employees on security protocols.
They should also establish clear legal action and law enforcement engagement plans.
What should a company do if confidential data is stolen?
If confidential information is stolen, a company should immediately launch a forensic investigation to identify the breach’s scope, notify law enforcement, and engage legal counsel.
Proactive public communication is also crucial to control the narrative.
How can allegations of unethical practices be addressed effectively?
Addressing allegations of unethical practices requires a two-pronged approach: a public denial of claims that are genuinely believed to be false and defamatory, while simultaneously conducting thorough internal investigations.
Fostering a transparent and fair internal culture can prevent such allegations from gaining traction or being weaponized.
Is it always wise for a tech CEO to deny all allegations publicly?
Publicly denying all allegations can be a valid strategy when claims are genuinely believed to be false and manipulated out of context.
However, such denials must be followed by concrete actions, like legal action and internal audits, to build credibility and maintain public trust.
Conclusion
The San Francisco fog, now lifted, reveals a new day, but the challenges facing a pioneering AI startup remain.
This experience is a stark reminder that building a groundbreaking AI company is not just about innovative technology or securing venture capital; it is about navigating an intricate web of human emotions, digital vulnerabilities, and ethical quandaries.
The quiet resolve required to face down an extortion threat while simultaneously addressing public allegations speaks to the immense pressures on modern tech leadership.
The story of this startup is still being written, but its unfolding chapters offer a profound lesson: true innovation must be matched by an equally robust commitment to integrity, security, and human-first leadership.
In this new era, the strongest foundations are not just built on code and capital, but on trust and unwavering ethical resolve.
It is time we build with this wisdom.